Cybersecurity
We bring enterprise Managed Services to non-enterprise customers
Cybersecurity & Disaster Recovery
Three pillars of Cybersecurity protection that keeps your Network in Shape
These three technologies are very significant individually, each playing a crucial role in network security. However, when integrated into a unified solution, they form a robust defense system that substantially increases the likelihood of withstanding and recovering from a cyber attack. This synergy allows the combined solution to leverage the strengths of each technology, mitigating their individual weaknesses and creating a multi-layered security approach that is far more effective than any of the technologies deployed in isolation.
Our affordable, enterprise-level services bring the power and efficiency of large-scale operations to smaller businesses, providing you with a competitive edge and fostering sustainable growth.
Virtualization
Benefits of Virtualization:
- Cost Savings: By running multiple virtual machines (VMs) on a single server, you can significantly reduce hardware costs and energy consumption.
- Scalability: Easily add or remove VMs to adapt to your business’s changing needs.
- Business Continuity: Safeguard your operations with multiple tier backups that ensure quick data and application recovery in case of a disaster.
- Flexibility: Seamlessly move VMs between servers and data centers to respond to evolving requirements.
How Does it Work?
The Future of IT
Cybersecurity
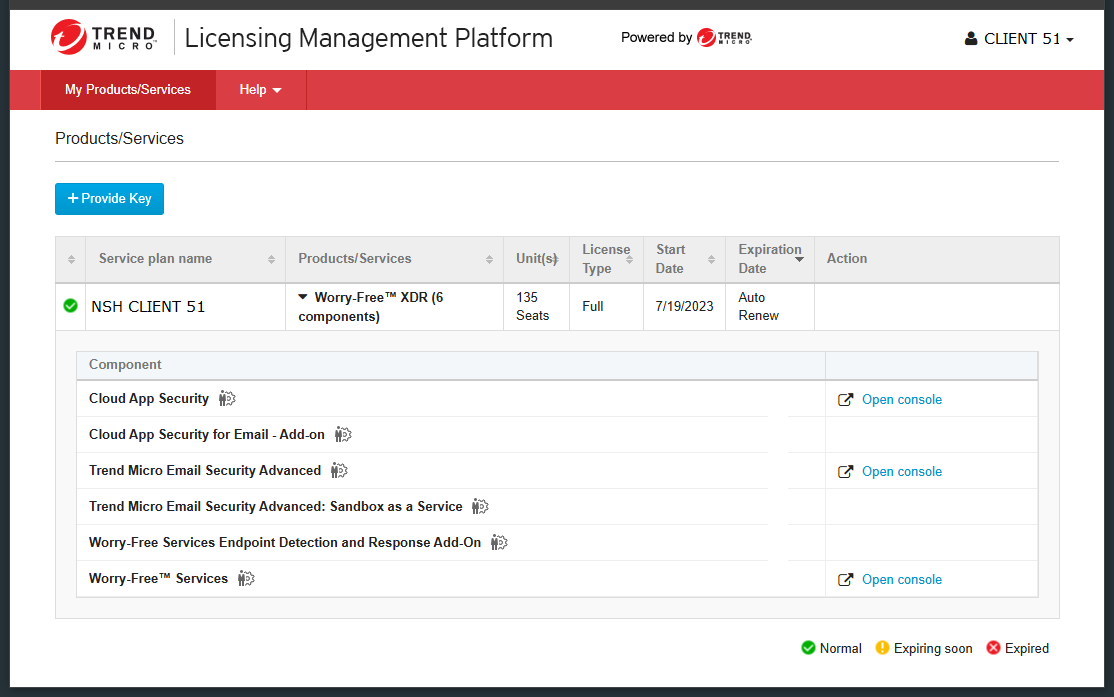
Our cybersecurity partner distinguishes itself as a select global entity, offering services to both small businesses and large enterprises.
As a Trend Micro partner we provide all layers of cybersecurity protection:
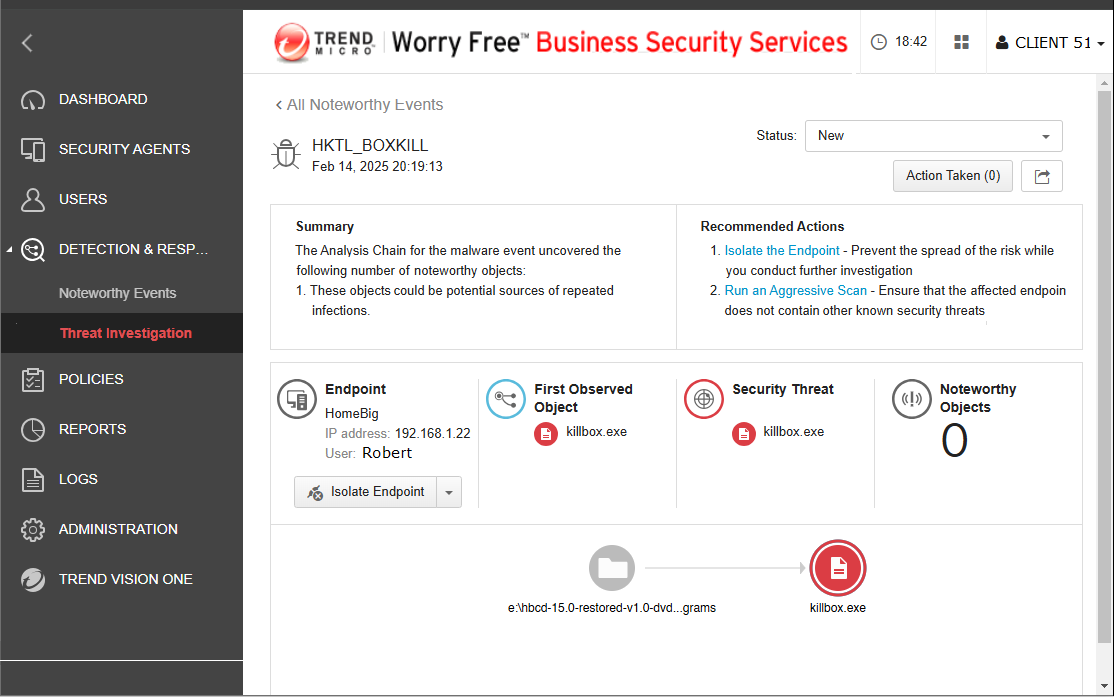
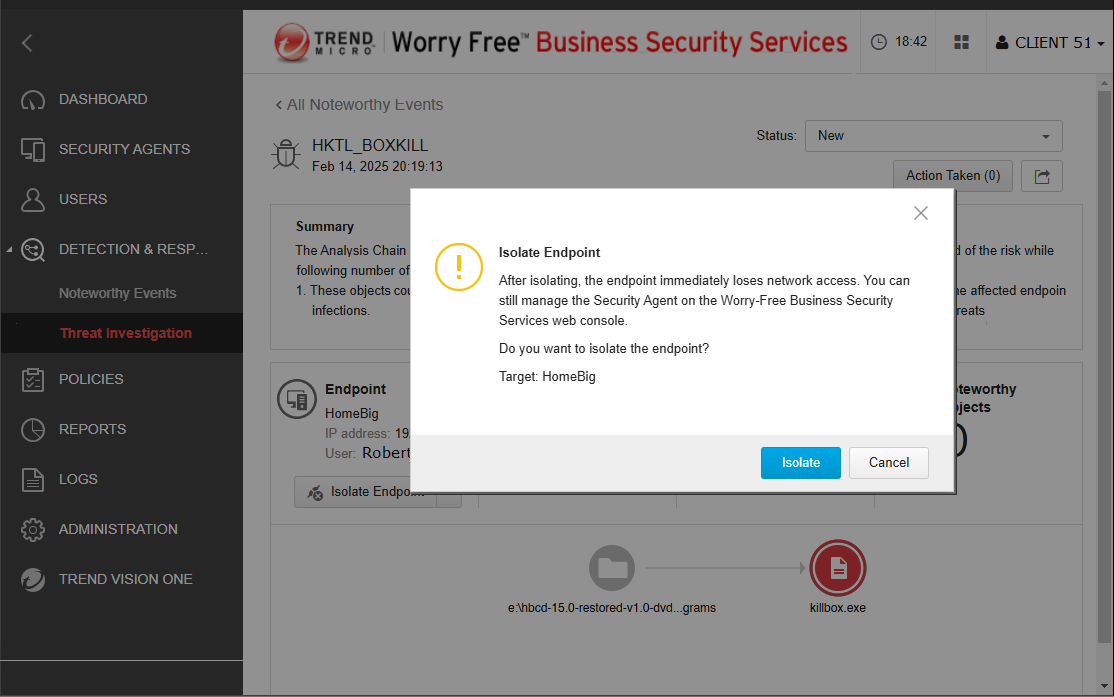
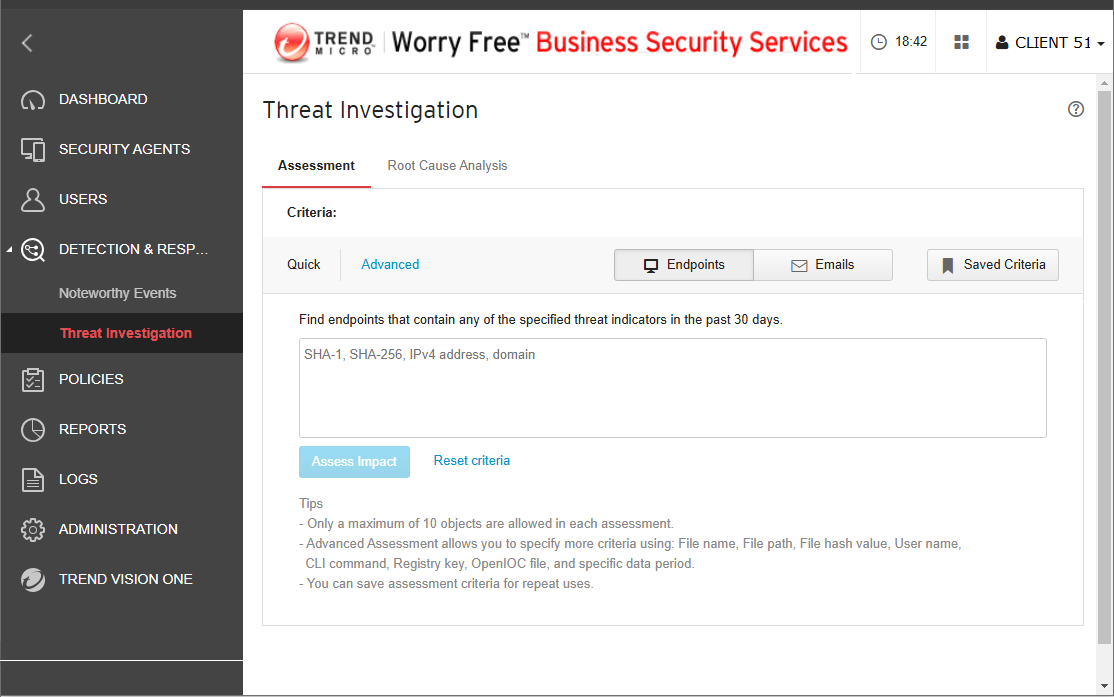
- EDR – endpoint detection and response
- XDR – extended detection and response, with endpoints isolation
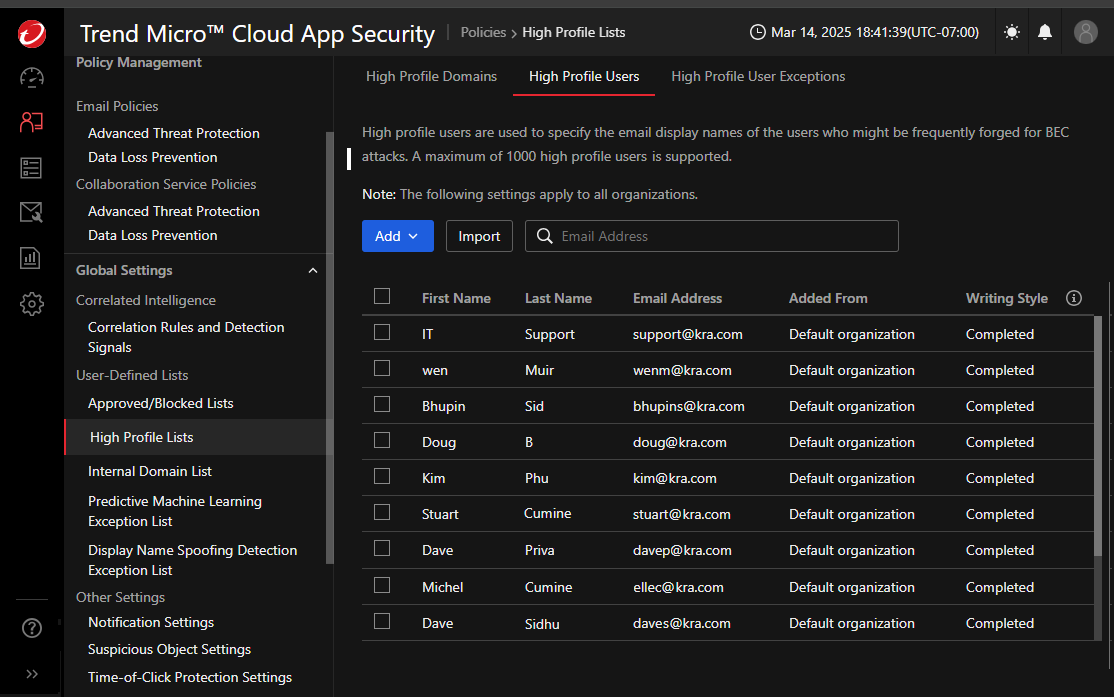
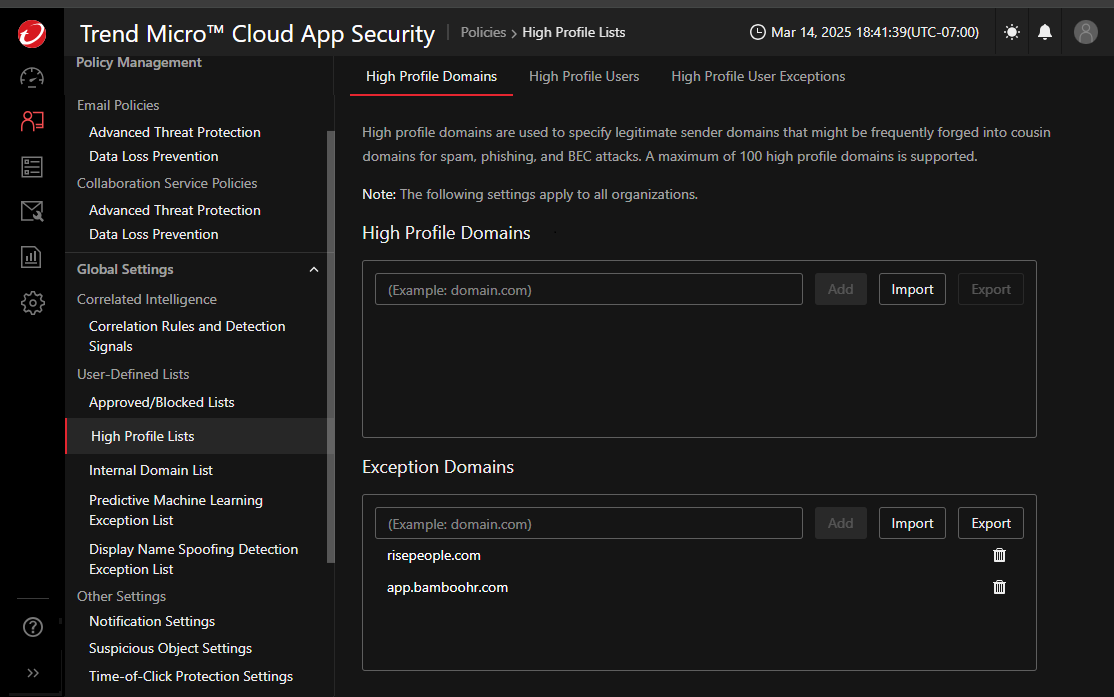
- Email security / Cloud App security – direct integration with Google Workspace and Office 365
- Impersonation protection for high profile users
- ASRM – Attack Surface Risk Management – endpoints continuous monitoring with individual LIVE risk assessment – ASRM is a pillar for Cyber Insurance Underwriting
- CREM – Cyber Risk Exposure Management
ASRM incorporates NDR (Network Detection and Response), EDR (Endpoint Detection and Response), Cloud Security and MDR (Managed Detection and Response). Together they deliver a solution that Transforms Cyber Insurance Underwriting.
CREM incorporates EM (Exposure Management), ASM (Attack Surface Management), EASM (External ASM), VRM (Vulnerability Risk Management), APA (Attack Path Analysis), SPM (Security Posture Management for: Cloud, SaaS, Data, AI, API, Identity), CRQ (Cyber Risk Quantification)
Cyber Risk Exposure Management is our proactive cyber risk solution, proactively uncovering, assessing, and mitigating threats to reduce your cyber risk footprint. It changes the narrative from a reactive to proactive approach to security.
Some Key benefits are:
- Unified experience for better understanding of your customer’s cyber risk posture
- Centralized visibility across identities, devices, cloud, APIs and more
- Continuous risk assessment to prioritize and mitigate risks in real time
- Predict and neutralize threats before they have a chance to materialize
- Optimize compliance and security configuration with risk-based insights
By embedding ASRM into the underwriting process, insurers can:
- Provide more accurate premium pricing: Real-time visibility into an organization’s security posture allows for risk-adjusted premiums based on actual exposure rather than static assessments.
- Reduce claims frequency and severity: Encouraging the adoption of advanced security technologies mitigates the likelihood of breaches, directly impacting the insurer’s bottom line.
- Enhance policyholder trust: Organizations that invest in ASRM demonstrate a commitment to cybersecurity, fostering stronger relationships with insurers.
ASRM Vision One
Actionable Insight Demo
Attack Surface Risk Management
Take Charge of Risk Demo
Disaster Recovery
Best practices require a disaster recovery plan that has a minimum of three different backups on two different repositories, one of which is offsite.
Depending on each client’s needs, we can perform some or all of the backup solutions below, going beyond minimum recommendations in safeguarding your data and business continuity.
Types of backups we perform:
- File Server backups to local repositories
- Virtual Machine backups to local repositories
- Virtual Machine backups to cloud repositories
- Endpoint backups to cloud repositories
- Google Workspace cloud backups for Accounts and Google Shared Drives
- Office 365 cloud backups for Accounts, One Drive and Sharepoint
Cloud repositories for Google Workspace, Office 365 and Endpoints retain backups for up to a year or indefinitely and are immune to cyberattacks on your network as there is no direct link between the two. Once written, the backups on the cloud repositories are read-only so they cannot be altered.
What clients say about our work
EXCELLENTTrustindex verifies that the original source of the review is Google. We have used NetworkShape for many years on our network, IT support, software & hardware maintenance. Dan & his team are always incredibly responsive & helpful in troubleshooting our issue. Their reliability and professionalism are top-notch. Kenneth from ALLCAN LogisticTrustindex verifies that the original source of the review is Google. Network Shape has been our IT support provider for the past ten years and I have found their services to be outstanding. After relocating my law office of 25 years I struggled to find a competent tech team for support. Interestingly, Network Shape was referred to us by Shaw Cable. Dan and Sergey provide exceptional service and have assisted us with all of our computer, telephone and IT needs. They make themselves available on short notice to resolve any problems we may have and also think strategically ahead on our behalf to prepare us for what we may need in the future. I have no hesitation in recommending them to any business. SAS & ING Immigration Law Centre Catherine A. Sas K.C.Trustindex verifies that the original source of the review is Google. We've been working with Dan and his team for the past 10 years. We are very happy with them. Dan and his team are very knowledgeable, friendly and helpful. Since we've been working with Dan, our IT has been running smoothly. Any issues that arise are dealt with right away. We are delighted with Dan and his team and look forward to continuing to work with him.Trustindex verifies that the original source of the review is Google. Great response time for all our company needs whether it's to set up a new user, trouble shoot, or tighten up cyber security. We have worked with Dan and his team for years and response time is so important with IT-related issues.Trustindex verifies that the original source of the review is Google. We trust Network Shape with our telephone and internet connection in three location. They were able to upgrade my mess of a IT equipment to a system that works in harmony at a reasonable cost. My only regret is I did not find them earlier.Trustindex verifies that the original source of the review is Google. NetworkShape has done IT & Communications for our school for 7 years. The staff have always been very professional and able to come up with solutions that are top notch.Trustindex verifies that the original source of the review is Google. NetworkShape designed and implemented our network infrastructure, equipping our offices with fully outfitted racks. They also installed a unified phone system that seamlessly integrates all our locations, supporting over 90 efficient office phones. This system enables effortless extension dialing across different locations while maintaining telephony costs within budget, ensuring a consistent monthly bill. NetworkShape's proactive approach ensures quick and dependable ticket response times.Trustindex verifies that the original source of the review is Google. Dan has been helping earth wind and fire for many years. His support and ability to help us grow has been what someone would expect but he excels in all of those qualities I mentioned above! Good luck Dan keep up the good work. Russ Steiner President/Owner EWF Services Inc Earth, Wind and FireTrustindex verifies that the original source of the review is Google. I was really happy with the solution that Network Shape came up with for my business, improving the efficacy of my email lists and more. Thank you Network Shape!Verified by TrustindexTrustindex verified badge is the Universal Symbol of Trust. Only the greatest companies can get the verified badge who has a review score above 4.5, based on customer reviews over the past 12 months. Read more




